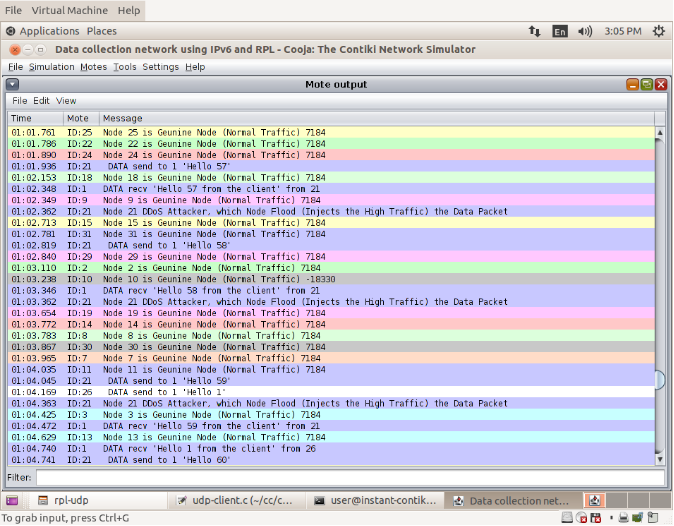
Unnecessary incoming traffic are originated from one source. This makes it an impossible to differentiates the normal data traffic from the DDOS flooding.
Open the file at location:
Contiki/examples/ipv6/
tpl-udp /udp-client.c -
Change the Interval,
#define PERIOD1 1
#define SEND_INTERVAL_1 (PERIOD1 * CLOCK_SECOND)
#define SEND_TIME_1 (random_rand() % (SEND_INTERVAL_1))
if (node_id == 21) {
ctimer_set(&backoff_timer, SEND_TIME_1, send_packet, NULL);
} else {
ctimer_set(&backoff_timer, SEND_TIME, send_packet, NULL);
}
Open cooja simulation
In terminal, go
to this directory: cd “contiki/
tools/ cooja/”
Give Command in terminal :
ant run
To create simulation.
Create motes for choose this
location server, client file.
/home/user/contiki/examples/
ipv6/rpl-udp
Run the simulation.
, Start- click run the simulation
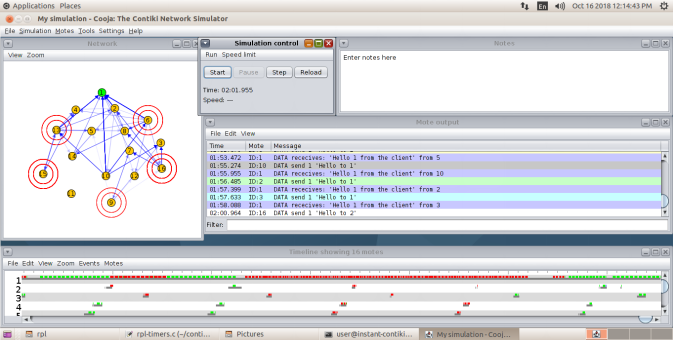
Normal Traffic