Transport Layer Protocols
The transport layer is next to the application layer. It is responsible for receiving data packets from the Network layer, reassembling the segmented data, identifying the port number by reading its header, and sending the message to the appropriate port in the Application layer. The main aims of the transport layer activities are to provide reliable communication, avoid network congestion, and guarantee the packet sequence during data transmission. The protocols used in the transport layer are TCP, UDP, and ICMP. The security protocols are TLS and DTLS. Some of the important features of transport layer protocols are discussed as follows.
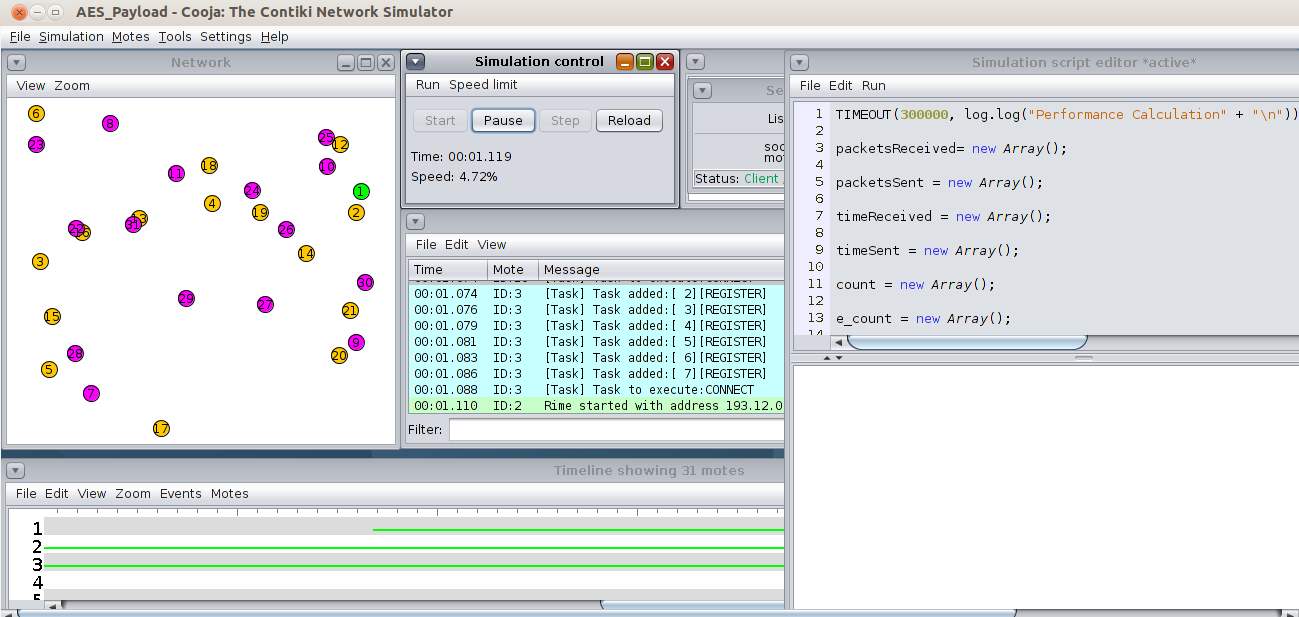
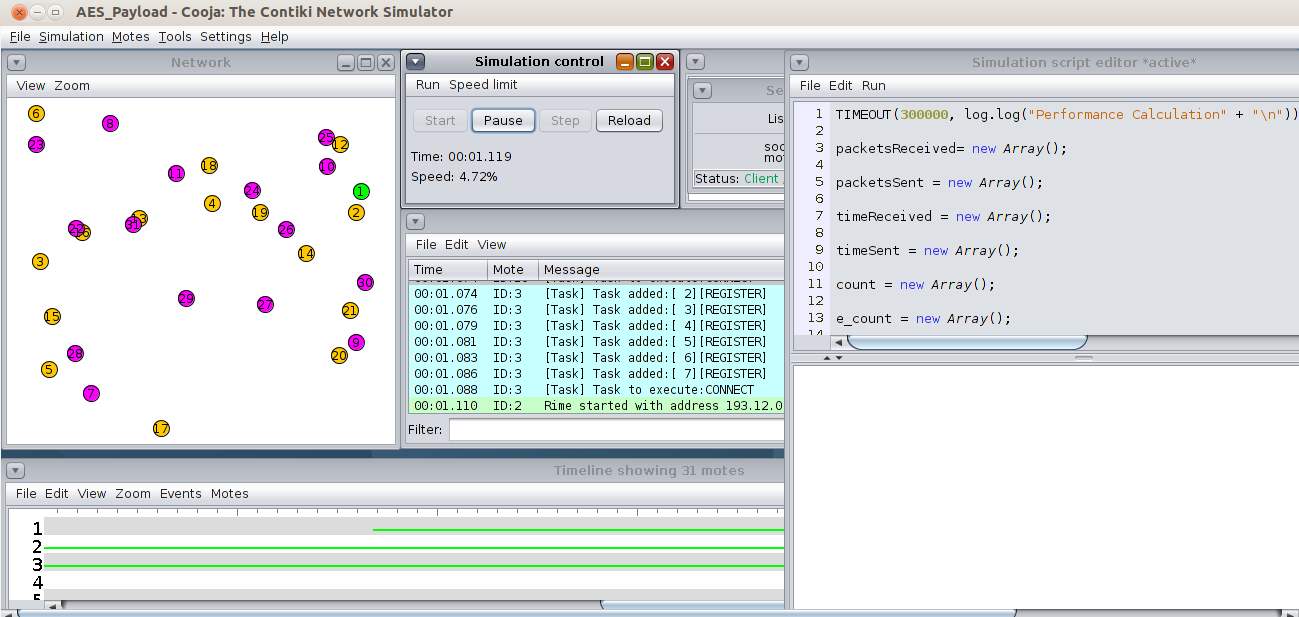
Working with TCP Protocol using Contiki Cooja Simulator
Transmission Control Protocol (TCP) is a reliable and connection-oriented protocol.
It is suitable for reliable communication due to the presence of the acknowledgment concept. If the packet is sent via the TCP protocol, it makes sure the data is sent to the other end via acknowledgment packet.
The protocol operates in three phases: establishing the connection, data transfer, and close connection.
An internet socket manages a TCP connection.
The packet overhead of TCP is high. TCP consumes more power from the devices and has a large overhead, so it is unsuitable for low-power devices with a constrained environment.
Working with UDP Protocol using Contiki Cooja Simulator
User Datagram Protocol is a connection-less protocol and is not reliable for guaranteed data transmission.
The UDP protocol returns better results when packet loss during data transmission can be afforded.
UDP protocol is a lightweight protocol and is suitable for tiny device communication.
Working with Transport Layer Security (TLS) Protocol using Contiki Cooja Simulator
Transport Layer Security (TLS) is a cryptographic protocol, and it offers end-to-end security of data sent between applications over the Internet.
TLS is built on TCP.
It can be used for several applications such as email, file transfers, video/audio conferencing, instant messaging, voice-over-IP, and Internet services.
The TLS handshake layer assumes that handshake messages are delivered reliably, and the connection is disconnected if messages get lost. Because its mission is to offer reliable communication and end-to-end encryption via TCP, it can’t be used to secure unreliable datagram traffic.
Working with Datagram Transport Layer Security (DTLS) using Contiki Cooja Simulator
Datagram Transport Layer Security (DTLS) is a stream-oriented transport layer protocol. It is based on the Transport Layer Security (TLS) protocol.
It is a security protocol designed against message forgery, tampering, and eavesdropping.
DTLS is built on UDP.
The main disadvantages of DTLS are large packet size, packet rearrangement, and loss of datagram.
DTLS is also designed to deliver authenticated and encrypted application data, enabling lower latency.